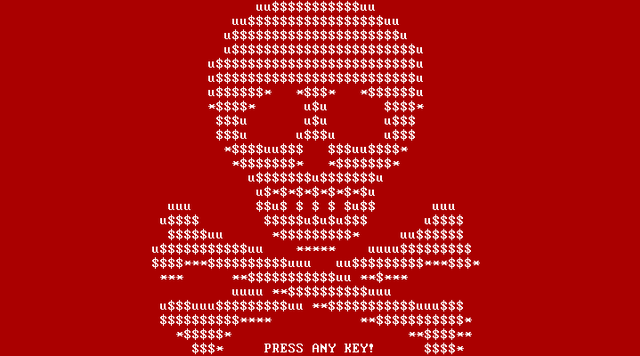
Attack description : The NotPetya ransomware attack of 2017 stands as one of the most destructive cyber incidents in history. This article delves into the technical intricacies of the attack, examining its propagation methods, infection vectors, and the destructive payload that crippled organizations worldwide.
Propagation and Infection Mechanisms: NotPetya employed multiple infection vectors to rapidly propagate within networks:
- Phishing Emails: The initial infections were often initiated through targeted phishing emails containing malicious attachments or links. Once a user fell victim to the phishing attempt and executed the payload, NotPetya gained a foothold on the victim’s system.
- Supply Chain Compromises: NotPetya took advantage of compromised software updates, infecting popular applications like tax accounting software. This enabled the malware to spread rapidly as unsuspecting users downloaded and installed the tainted updates.
- EternalBlue Exploit: Similar to the WannaCry attack, NotPetya utilized the EternalBlue exploit, which targeted a vulnerability in the SMB protocol. The exploit allowed the malware to move laterally across vulnerable systems within the same network.
Destructive Payload and Data Overwrite: NotPetya differed from traditional ransomware in that it was primarily designed as a destructive tool rather than a means to extort ransom payments. Upon infecting a system, NotPetya employed a multi-stage process:
- MBR Overwrite: The malware overwrote the Master Boot Record (MBR) with a custom bootloader, effectively preventing the system from booting. This made the infected machine unusable and caused significant disruption.
- MFT Encryption: NotPetya encrypted the Master File Table (MFT), which contains crucial information about file locations on the disk. This rendered the file system inaccessible, further increasing the difficulty of data recovery.
- Network Propagation: NotPetya utilized legitimate administrative tools like PsExec and WMI to propagate across the network, infecting other vulnerable devices. This lateral movement facilitated the rapid spread of the malware within organizations.
Impact: The NotPetya ransomware attack had far-reaching technical consequences:
- Operating System Tampering: By overwriting the MBR and encrypting the MFT, NotPetya rendered infected systems inoperable, disrupting critical operations and causing significant financial losses.
- Data Loss and Recovery Challenges: The destructive nature of NotPetya made data recovery extremely difficult, especially without comprehensive backups. Many organizations faced permanent data loss and had to rebuild their systems from scratch.
- Pseudorandom Algorithm: NotPetya employed a pseudorandom algorithm for generating encryption keys, making decryption without the original key practically impossible. This added to the complexity of recovery efforts.
Mitigation Strategies: The NotPetya attack highlighted several critical lessons for the cybersecurity community:
- Patch Management: Organizations must prioritize timely patching to address known vulnerabilities. Regularly applying security updates helps mitigate the risk of exploitation.
- Network Segmentation and Access Controls: Implementing strong network segmentation limits the lateral movement of malware within a network, preventing widespread infections.
- Incident Response Preparedness: Developing robust incident response plans and conducting regular exercises enables organizations to respond effectively in the event of an attack, minimizing damage and facilitating recovery.
- Backup and Recovery: Regularly backing up critical data and storing backups offline ensures the ability to restore systems in the event of a cyber attack. Testing backups for integrity is equally important.
- Enhanced Employee Awareness: Continuous cybersecurity training and awareness programs educate employees about phishing attacks, suspicious attachments, and safe online practices, reducing the risk of inadvertent malware execution.
Take away: The NotPetya ransomware attack of 2017 showcased the destructive potential of advanced malware and its ability to disrupt organizations on a global scale. By understanding the technical intricacies of the attack and implementing proactive cybersecurity measures, organizations can fortify their defenses, reduce vulnerabilities, and minimize the devastating impact of future cyber threats. Emphasizing patch management, network segmentation, incident response preparedness, and employee awareness remains critical in mitigating the risks posed by sophisticated ransomware attacks like NotPetya.
Disclaimer : The information provided herein is on “as is” basis, without warranty of any kind.