Calendar Vulnerabilities and Exploits: Like any other software or application, the calendar app on Android devices may contain vulnerabilities that hackers can exploit. These vulnerabilities can be used to gain unauthorized access to the device’s calendar and potentially compromise personal and professional information. Hackers may employ various techniques, such as malware, phishing attacks, or exploiting security flaws, to infiltrate the calendar app.
Mitigation Measures:
While the risks of hacking through the calendar on Android devices exist, there are several measures you can take to enhance your device’s security:
- Keep Your Device Updated: Regularly update your Android device’s operating system and applications, including the calendar app. Updates often contain important security patches that address known vulnerabilities.
- Download Apps from Trusted Sources: Stick to official app stores like Google Play Store and avoid sideloading apps from unknown sources. Official stores have security measures in place to minimize the presence of malicious apps.
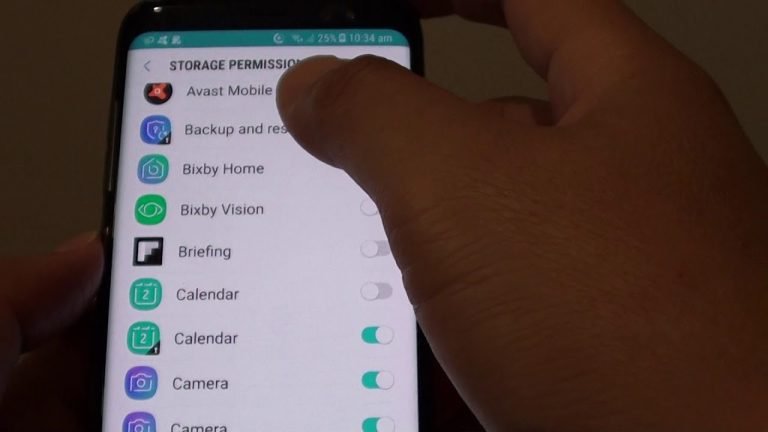
- Exercise Caution with App Permissions: Before granting calendar permissions to any app, carefully evaluate the necessity of such access. Be mindful of apps that request unnecessary permissions and consider using permission control features provided by the Android operating system.
- Install Antivirus and Security Software: Utilize reputable antivirus and security software on your Android device. These programs can help detect and mitigate potential threats, including malware targeting your calendar app.
- Enable Lock Screen Security: Protect your device with a strong PIN, password, pattern, or biometric authentication method. This adds an extra layer of security and prevents unauthorized access to your device and its calendar.
- Be Wary of Phishing Attempts: Stay vigilant against phishing attacks through emails, text messages, or suspicious links. Avoid clicking on unknown links or providing personal information unless you can verify the source’s authenticity.
- Backup Your Data: Regularly backup your calendar data to a secure location, such as cloud storage or a computer. In case of a security breach or data loss, having backups ensures you can recover your important information.
Impact of Body Sensors Hacking:
- Privacy Breach: Hackers can obtain sensitive information from your calendar, such as personal appointments, meetings, location data, and contact details. This information can be used for targeted attacks, identity theft, or even blackmail.
- Data Manipulation: Unauthorized access to your calendar allows hackers to modify or delete events, potentially leading to confusion, missed appointments, or disrupted schedules. This can have negative consequences both personally and professionally.
- Social Engineering Attacks: Knowledge of your calendar events can provide hackers with valuable insights into your routines, enabling them to craft convincing social engineering attacks. They can use this information to trick you into revealing further sensitive information or performing actions that compromise your security.
We will understand how to use and avoid each type of permission in upcoming articles
Post Views: 826