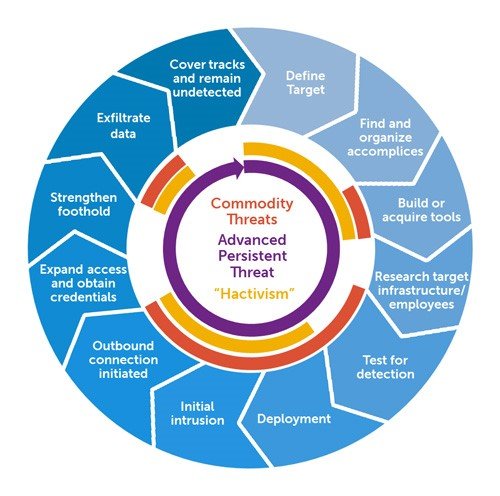
Attack & attackers description : SandWorm is an elusive and persistent state-sponsored cyber espionage group that has been active since 2013. Known for its sophisticated tactics and targeted operations, SandWorm has primarily focused on infiltrating critical infrastructure and government entities. This technical article delves into the advanced techniques and notable campaigns attributed to the SandWorm group, highlighting the group’s modus operandi and the implications for cybersecurity.
Advanced Techniques and Operations:
- Zero-Day Exploits: SandWorm has demonstrated a keen ability to discover and exploit zero-day vulnerabilities, leveraging previously unknown software flaws to infiltrate targeted systems. The group’s expertise in finding these vulnerabilities allows them to bypass security measures and gain privileged access to compromised networks.
- Watering Hole Attacks: SandWorm has been associated with “watering hole” attacks, where they compromise legitimate websites frequently visited by their targets. By injecting malicious code into these websites, they can deliver tailored malware to unsuspecting visitors, effectively infiltrating their systems and establishing a foothold for further exploitation.
- PowerShell Exploitation: The group heavily relies on the abuse of PowerShell, a powerful scripting language embedded in the Windows operating system. By utilizing PowerShell-based exploits and frameworks, SandWorm bypasses traditional security measures and maintains stealthy persistence within compromised networks.
- Supply Chain Attacks: SandWorm has demonstrated a sophisticated understanding of software supply chains, exploiting weaknesses in third-party software vendors. By compromising legitimate software updates or injecting malicious code into software packages, they gain backdoor access to target organizations, bypassing traditional perimeter defenses.
Impacts of Campaigns:
- BlackEnergy: SandWorm gained significant attention for its involvement in the BlackEnergy campaign. In 2015, the group launched a series of cyber attacks against Ukraine’s energy sector, resulting in widespread power outages. These attacks highlighted the potential for cyber attacks to disrupt critical infrastructure.
- Telecommunications Sector Exploitation: SandWorm has targeted telecommunications companies in Eastern Europe, leveraging their networks for reconnaissance and facilitating future operations. By compromising these networks, the group gains access to sensitive communications data and potentially conducts espionage activities.
- Olympic Destroyer: SandWorm was also linked to the Olympic Destroyer malware, which disrupted the opening ceremony of the 2018 Winter Olympics in PyeongChang, South Korea. This highly sophisticated malware targeted critical infrastructure and disrupted network operations, causing significant disruptions and casting suspicion on other nation-states.
Mitigations : The activities of SandWorm raise important implications for cybersecurity and the protection of critical infrastructure:
- Enhanced Detection and Response: Detecting SandWorm’s advanced techniques requires robust monitoring and analysis of network traffic, including anomaly detection and behavioral analysis. Implementing advanced threat detection systems and investing in skilled incident response teams is crucial to identifying and mitigating SandWorm’s attacks.
- Vulnerability Management: Given SandWorm’s adeptness at exploiting zero-day vulnerabilities, organizations must prioritize vulnerability management practices. Regular patching and timely software updates are essential to minimize the attack surface and reduce the risk of exploitation.
- Supply Chain Security: Organizations should implement stringent controls and verification processes within their software supply chains. Conducting thorough security assessments of third-party vendors and validating the integrity of software updates can help mitigate the risk of supply chain attacks.
- Threat Intelligence Sharing: Collaborative efforts between government agencies, cybersecurity organizations, and the private sector are vital in combating state-sponsored cyber threats like SandWorm. Sharing actionable threat intelligence helps identify emerging attack patterns and strengthens collective defenses against such advanced adversaries.
Take away: SandWorm’s activities demonstrate the evolving capabilities of state-sponsored cyber espionage groups and their potential to disrupt critical infrastructure. The group’s advanced techniques, including
Disclaimer : The information provided herein is on “as is” basis, without warranty of any kind.