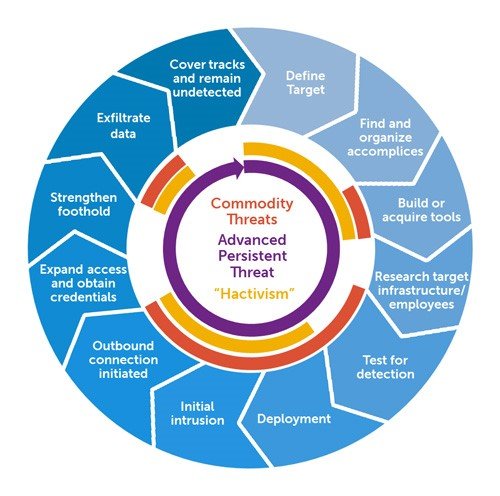
Attack & attackers description :Operation Ababil, an infamous cyber attack campaign spanning 2012 to 2013, showcased the power and sophistication of distributed denial of service (DDoS) attacks. Specifically targeting major financial institutions in the United States, this operation marked a significant escalation in the tactics and scale of hacktivist-driven cyber assaults. This technical article explores the intricacies of Operation Ababil, shedding light on the advanced techniques employed, the impact on the targeted organizations, and the broader implications for DDoS defense strategies.
Operation Ababil demonstrated a high level of sophistication in executing large-scale DDoS attacks against prominent financial institutions. Here are the key technical aspects of the operation:
- Botnet Coordination: The attackers skillfully leveraged botnets, vast networks of compromised computers, to orchestrate their attacks. These botnets, comprising tens of thousands of hijacked computers, acted as a formidable force for generating massive volumes of malicious traffic aimed at overwhelming the targeted banks’ networks.
- Layered DDoS Attacks: Operation Ababil employed both network-layer and application-layer DDoS attacks. The network-layer attacks targeted the banks’ network infrastructure, exploiting vulnerabilities in protocols like the Transmission Control Protocol (TCP) or User Datagram Protocol (UDP). Simultaneously, application-layer attacks focused on the web servers, aiming to exhaust server resources by overwhelming them with malicious requests.
- Amplification Techniques: To maximize the impact of their attacks, the hackers employed various amplification techniques. These techniques involved exploiting vulnerabilities in internet protocols, such as the Domain Name System (DNS), Simple Network Management Protocol (SNMP), or Network Time Protocol (NTP). By abusing these protocols, the attackers amplified their attack traffic, magnifying the impact on the targeted organizations.
Impact :
Operation Ababil had far-reaching consequences for the financial institutions targeted and led to significant advancements in DDoS defense strategies. Here are the primary effects and subsequent countermeasures:
- Disruption and Financial Losses: The DDoS attacks launched during Operation Ababil caused significant disruptions to the targeted banks’ online services, rendering them inaccessible to customers. This led to potential financial losses due to the inability to process transactions or provide uninterrupted services.
- Enhanced DDoS Mitigation: Operation Ababil served as a wake-up call for financial institutions, pushing them to invest in more robust DDoS mitigation measures. These included the deployment of dedicated DDoS protection services, collaboration with cloud-based scrubbing centers, and the adoption of intelligent traffic analysis systems capable of identifying and filtering out malicious traffic.
- Collaborative Defense Efforts: Operation Ababil prompted collaboration among targeted organizations, government agencies, and cybersecurity firms. Sharing threat intelligence, coordinating response efforts, and establishing incident response teams became critical components in mitigating and countering DDoS attacks effectively.
- Advanced Traffic Analysis: The attacks highlighted the need for more advanced traffic analysis and anomaly detection systems. Organizations began leveraging machine learning algorithms and behavioral analysis techniques to identify and respond to DDoS attacks in real-time, enabling faster mitigation and minimizing service disruptions.
Mitigations & response : Operation Ababil, the targeted banks collaborated with government agencies and cybersecurity firms to enhance their DDoS defenses and implement measures to mitigate future attacks. The incident prompted increased awareness of the importance of robust DDoS protection and the need for financial institutions to invest in resilient infrastructure and response capabilities to withstand such attacks.
Take away: Operation Ababil represented a significant milestone in the evolution of DDoS attacks, showcasing the growing capabilities of hacktivist-driven cyber assaults. This campaign exposed vulnerabilities in the financial sector’s online infrastructure and pushed organizations to adopt more sophisticated DDoS defense strategies. As cyber threats continue to evolve, staying ahead of adversaries necessitates ongoing investment in advanced DDoS mitigation techniques, collaborative defense efforts, and the continuous enhancement of traffic analysis capabilities. By doing so, organizations can fortify their cyber defenses, ensuring the availability and reliability of critical online services in
Disclaimer : The information provided herein is on “as is” basis, without warranty of any kind.